Inter-Service Communication in Microservices
Last Updated :
18 Sep, 2025
Microservices architecture breaks a large application into small, independent services that work together. These services must communicate to exchange data and perform business operations. Inter-Service Communication is the backbone of microservices, ensuring services remain loosely coupled yet fully functional as part of the larger system.
 Inter-Service Communication
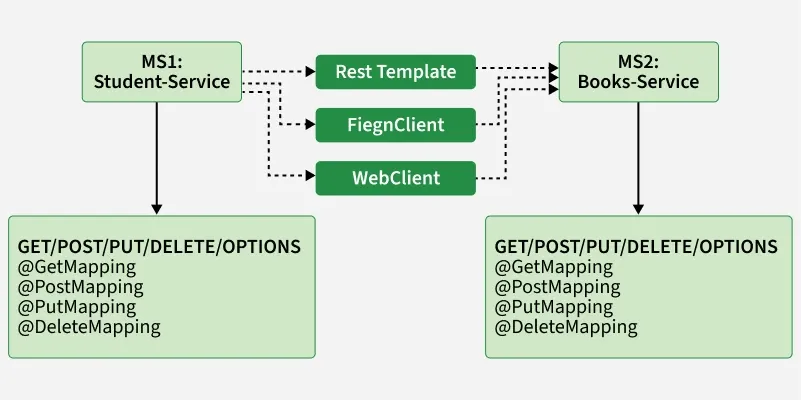
Inter-Service Communication This image shows inter-service communication in microservices.
- MS1: Student-Service communicates with MS2: Books-Service.
- Services expose endpoints using @GetMapping, @PostMapping, @PutMapping and @DeleteMapping.
- Communication happens through three approaches: RestTemplate, FeignClient and WebClient.
- Each client acts as a connector to make HTTP calls between the microservices.
The choice of communication style impacts:
- Performance
- Scalability
- Fault tolerance
- System complexity
Types of Inter-Service Communication in Microservices
Inter-Service Communication in microservices can be broadly categorized into two main types: synchronous and asynchronous communication. Each type has its methods, protocols and use cases:
1. Synchronous Communication
- Real-time, request-response communication.
- Commonly implemented via REST APIs (HTTP), gRPC or GraphQL.
- Example: Student-Service calls Books-Service using REST to fetch available books.
2. Asynchronous Communication
- Services communicate without waiting for an immediate response.
- Implemented using Message Queues (RabbitMQ, Kafka, ActiveMQ).
- Example: Student-Service publishes an event "Student Registered" and Books-Service consumes it later.
3. Hybrid Communication
- Combination of synchronous and asynchronous methods.
- Used when certain operations require real-time responses, while others can be event-driven.
Example:
- Student-Service sends a synchronous REST request to Books-Service to fetch a list of available books.
- At the same time, Student-Service publishes an event asynchronously (Student Borrowed Book) so other services (like Notification-Service or Analytics-Service) can react later.
Implementation Approaches in Spring Boot
1. RestTemplate (Legacy, Synchronous): A legacy, synchronous, blocking HTTP client for service-to-service calls.
Java
RestTemplate restTemplate = new RestTemplate();
String result = restTemplate.getForObject(
"http://books-service/books/1", String.class);
Note: RestTemplate is officially deprecated in Spring 5+. Use WebClient for new applications
2. Feign Client (Declarative, Synchronous): A declarative REST client with built-in load balancing and cleaner syntax.
Java
@EnableFeignClients
@SpringBootApplication
public class StudentServiceApplication { }
@FeignClient(name = "books-service")
public interface BookClient {
@GetMapping("/books/{id}")
Book getBook(@PathVariable("id") Long id);
}
3. WebClient (Reactive, Asynchronous): A modern, reactive, non-blocking HTTP client for async communication.
Java
WebClient client = WebClient.create("http://books-service");
Book book = client.get()
.uri("/books/1")
.retrieve()
.bodyToMono(Book.class)
.block();
Communication Patterns in Microservices
Communication patterns in microservices define how services interact with each other to achieve specific tasks. These patterns help manage the complexity of distributed systems, ensuring that services communicate efficiently and reliably. Below are some common communication patterns in microservices:
1. Request-Response Pattern
- One service sends a request and waits for a response (synchronous).
- Use Case: Immediate replies like fetching user details or processing payments.
- Examples: REST, gRPC, SOAP.
2. Publish-Subscribe Pattern:
- Services publish events to a broker; subscribers react asynchronously.
- Use Case: Notify multiple services of events (e.g., new user registration).
- Examples: Kafka, AWS SNS, Google Pub/Sub.
To Know more about Publish-Subscribe Pattern: -> Publish-Subscribe Pattern
3. Event Sourcing Pattern
- State is derived by replaying a sequence of stored events.
- Use Case: Maintaining full history (e.g., audits, financial transactions).
- Examples: EventStoreDB, Kafka event streams.
To Know more about Event Sourcing Pattern -> Event Sourcing Pattern
4. CQRS (Command Query Responsibility Segregation) Pattern
- Separates write (commands) and read (queries) operations.
- Use Case: Optimize reads/writes in complex systems.
- Examples: Different databases for read and write.
To Know more about CQRS -> CQRS (Command Query Responsibility Segregation) Pattern
5. Circuit Breaker Pattern
- Stops repeated calls to failing services and allows recovery later.
- Use Case: Prevent cascading failures and improve resilience.
- Examples: Hystrix, Resilience4j.
To Know more about Circuit Breaker Pattern -> Circuit Breaker Pattern
6. Saga Pattern
- Breaks long transactions into smaller compensating steps across services.
- Use Case: Distributed transactions (e.g., order processing).
- Examples: Orchestrated or Choreographed Sagas.
To Know more about Saga Pattern -> Saga Pattern
7. API Gateway Pattern
- Single entry point for clients; handles routing, security, logging and rate limiting.
- Use Case: Simplify client interactions with multiple services.
- Examples: Netflix Zuul, Amazon API Gateway, Kong.
To Know more about API Gateway Pattern -> API Gateway Pattern
8. Backend for Frontend (BFF) Pattern
- Separate backends for different clients (mobile, web).
- Use Case: Custom APIs per client type for efficiency.
- Examples: Custom BFF microservices.
9. Strangler Pattern
- Replace legacy systems gradually by introducing new microservices alongside them.
- Use Case: Safe modernization without a complete rewrite.
- Examples: Migrating modules like payments or user services step by step.
To Know more about Strangler Pattern -> Strangler Pattern
10. Service Mesh Pattern
- Infrastructure layer managing service-to-service communication (load balancing, auth, monitoring).
- Use Case: Large-scale microservice security and observability.
- Examples: Istio, Linkerd, Consul.
To Know more about Strangler Pattern -> Service Mesh Pattern
Security in Inter-Service Communication
In microservices, the distributed nature increases the attack surface, making secure communication essential to protect data, ensure confidentiality and prevent unauthorized access.
Key Strategies
1. Authentication & Authorization
- Authentication: Verify service identity using mTLS (mutual TLS) or OAuth2/JWT tokens.
- Authorization: Enforce RBAC (role-based) or PBAC (policy-based) access controls.
2. Encryption
- In Transit: Use TLS for all service-to-service communication.
- At Rest: Encrypt sensitive stored data.
3. Service Mesh
- Use tools like Istio/Linkerd for uniform security.
- Enforce mTLS and fine-grained access policies automatically.
4. API Gateway Security
- Centralize security with rate limiting, IP whitelisting, input validation.
- Validate JWT tokens before requests reach services.
- Enable logging & monitoring for auditing and threat detection.
5. Security Headers
- Apply CSP, HSTS, X-Content-Type-Options for web safety.
- Configure CORS to prevent CSRF and unauthorized domain access.
Best Practices for Inter-Service Communication in microservices
Implementing effective inter-service communication in microservices requires a set of best practices to ensure that the system remains scalable, reliable and maintainable. Here are some of the best practices to follow:
- Synchronous vs. Asynchronous: Use synchronous communication (e.g., REST, gRPC) for real-time, request-response interactions and asynchronous communication (e.g., message queues, event streams) for decoupling services and improving scalability.
- Protocol Selection: Choose communication protocols that match the requirements of your services. REST is widely used for HTTP-based interactions, while gRPC offers lower latency and better performance for high-throughput scenarios.
- Circuit Breaker Pattern: Use circuit breakers to prevent cascading failures by stopping repeated attempts to call a failing service. This helps to protect the system from being overwhelmed.
- Data Minimization: Transfer only the necessary data between services to reduce payload size and improve performance.
- Compression: Use data compression techniques for large payloads to reduce the amount of data transmitted over the network.
- Token-Based Authentication: Use OAuth2 or JWT tokens for secure authentication and authorization between services.
Challenges in Inter-Service Communication in Microservices
Due to their distributed nature, microservices face several communication challenges that affect performance, reliability and maintainability:
- Network Latency & Reliability: Network calls introduce latency and risk of failures, unlike in-process communication in monoliths.
- Data Consistency: Ensuring consistency across distributed services is hard, often relying on eventual consistency.
- Service Discovery: Dynamic scaling makes locating the correct service instance complex without proper discovery mechanisms.
- Failure Handling: Independent service failures can cascade; requires retries, timeouts and circuit breakers.
- Load Balancing and Scalability: Distributing traffic evenly across service instances is difficult but critical for performance.
- Security: Service-to-service communication across environments needs strong measures (e.g., TLS, authentication) to prevent attacks.
- Testing Complexity: Testing multi-service, async flows is harder than monolith testing. Integration testing, contract testing and chaos testing help improve reliability.
Explore
What is System Design
System Design Fundamentals
Scalability in System Design
Databases in Designing Systems
High Level Design(HLD)
Low Level Design(LLD)
Design Patterns
Interview Guide for System Design
System Design Interview Questions & Answers