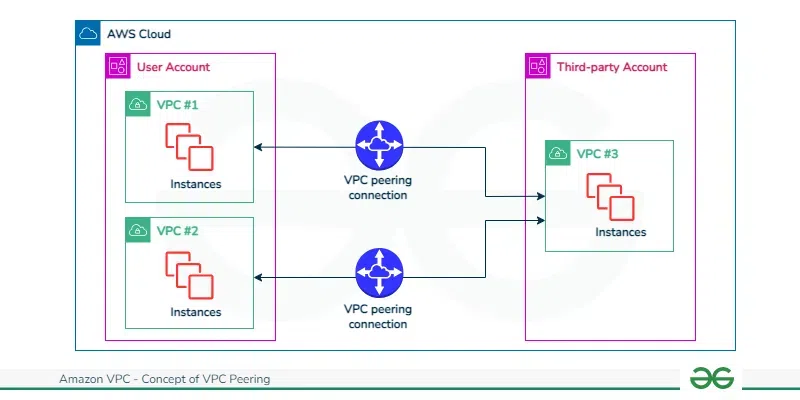
VPC Peering is a networking connection between two VPCs that enables you to route traffic between them using private IPv4 or IPv6 addresses. Instances in either VPC can communicate with each other as if they were within the same network.
It is the simplest way to connect two VPCs, whether they are in the same AWS account or different accounts, and even across different AWS Regions.
How VPC Peering Works
When you peer two VPCs (let's call them VPC A and VPC B), you create a direct network route between them.
- Private Connectivity: Traffic between peered VPCs stays on the AWS global backbone. It never traverses the public internet, ensuring security and high bandwidth.
- No Gateways: Unlike VPNs, there is no "gateway" or device to manage. It is a logical connection defined in the routing tables.
Architecture: One-to-One Connection
VPC Peering is strictly a 1:1 relationship. This is its most critical architectural feature.
- Non-Transitive: If VPC A is peered with VPC B, and VPC B is peered with VPC C, VPC A cannot talk to VPC C.
- The Mesh Problem: To connect A, B, and C fully, you need three separate peering connections (A-B, B-C, A-C). As you add more VPCs, the number of connections grows exponentially ($N(N-1)/2$), which becomes unmanageable at scale.
AWS VPC Peering Connection Lifecycle
The lifecycle of AWS VPC peering connection involves with serval key stages. Those are discuss as follow:
- Initiation: The life cycle process starts with initating a request to peer two VPCs. This request involves with specifying the VPCs to be peered and their respective settings.
- Approval: After the request is raised, the adminstrator of the receiving VPC have to accept that peering connection. This step involves both the parties to agress the connection establishment.
- Establishment: One Both approved the peering connection, the VPC peering connection is established. This enables the communication between two VPCs, if they were within same network, i.e., allowing instances in one VPC to communicate with other VPC's instance using private IP address.
- Configuration: After once, the connection is established, adminstrator may ensure configuring the route tables and security groups to control flow of the traffic between peered VPCs. This steps ensure the communication should be done in secured and follow with desired network paths.
- Utilization: With this peered connections, the resources within the peered VPCs can communicate with each other seamlessly. This provides various use cases such as data replication, resource sharing and application integration across multiple VPCs.
- Monitoring And Maintenance: Adminstrators continuously monitor the performance and security of the VPC peering connection. They may also perform the maintenance tasks such as updating route tables or adjusting security group rules as needed to optimize the connection's performance and ensuring its reliability.
- Termination ( Optional ): If need arises, the adminstrators can look for terminating the VPC peering connection. This effectively serves as the network link between the VPCs and prevents further communication between them.
How VPC Peering Works: Multi-VPC Connections
Multiple VPC peering connections are allowed for a network toplogy where multiple Virtual Private Clouds (VPCs) are interconnected. This provides the granular control over the communication between components or environments within an organization's cloud infrastructure. Each peering operates independent chanels and security configurations between specific VPC pairs. Adminstators can strategically deploy and manage mutiple peering connections to support many use cases such as multi-tiered application architectures, segregated development environments or distributed microservices deployments.

These VPCs can be in different regions and are hence known as inter-region VPC Peering connections.
How to Setup AWS VPC Peering Connections: A Step-By-Step Guide
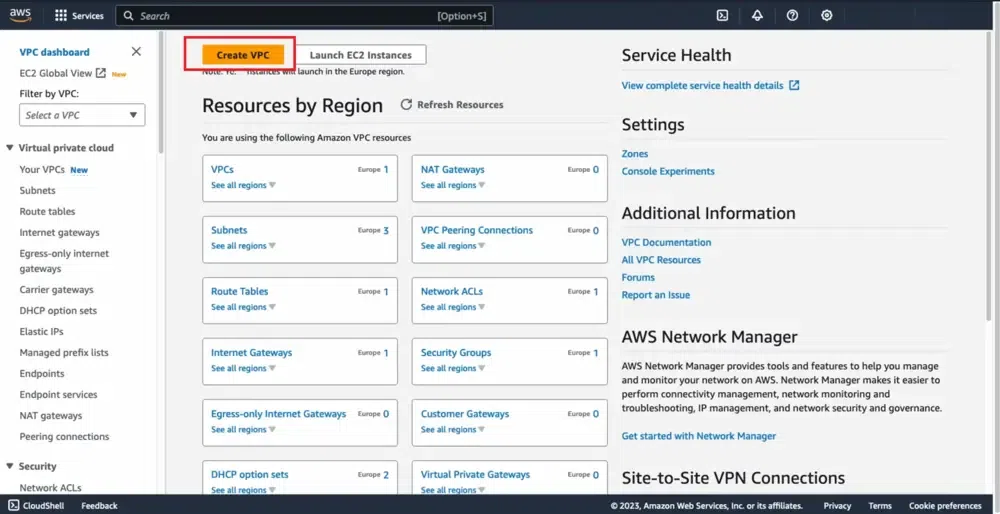
Step 1: Navigate to VPC Dashbaord
- Sign in to your AWS account with your credentials.
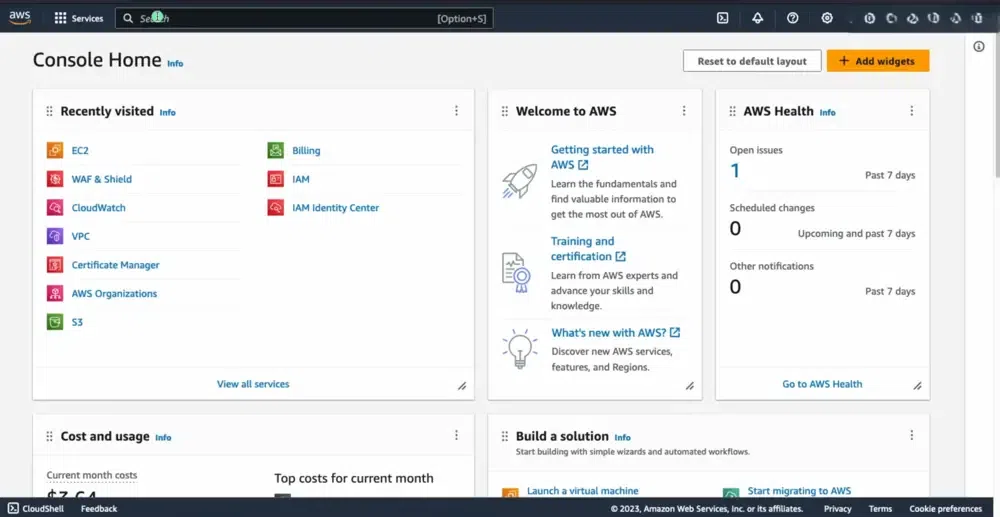
- After Navigate to Console, you look into the following Console Home Page
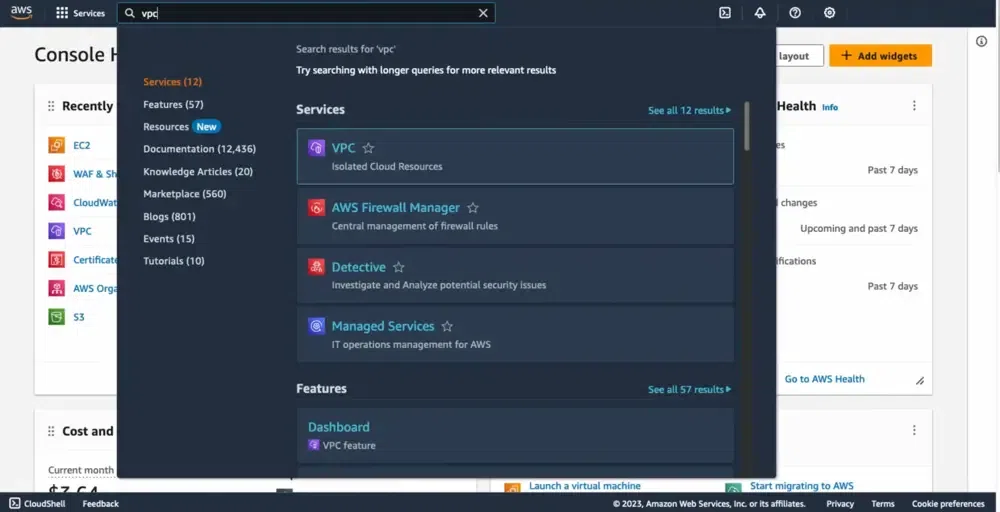
- Select the VPC service in the search box.
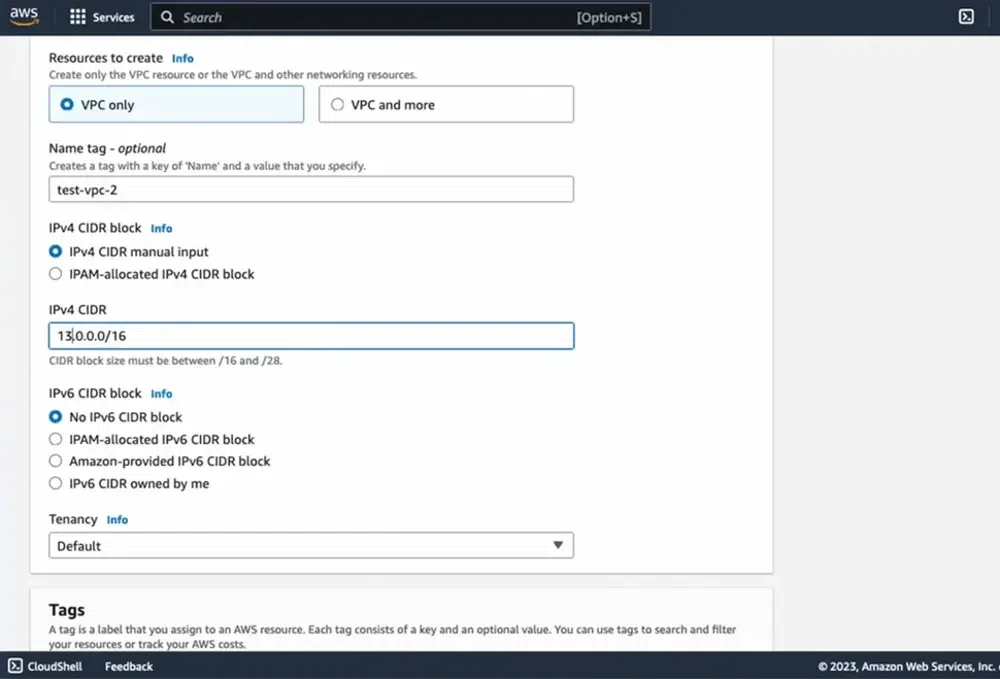
Step 2: Create Virtual Private Network
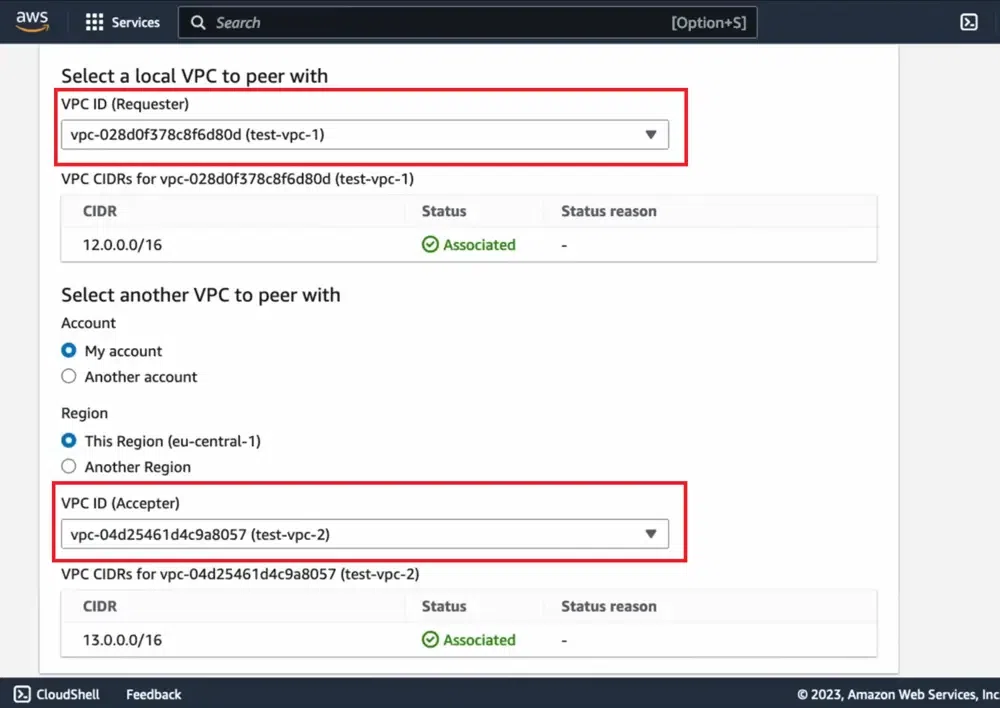
- Create 2 VPC networks with names test-vpc-1 and test-vpc-2.
- Firstly, Click on the Create VPC button to create VPC.
- Configure the VPC details as shown in the below screenshot.
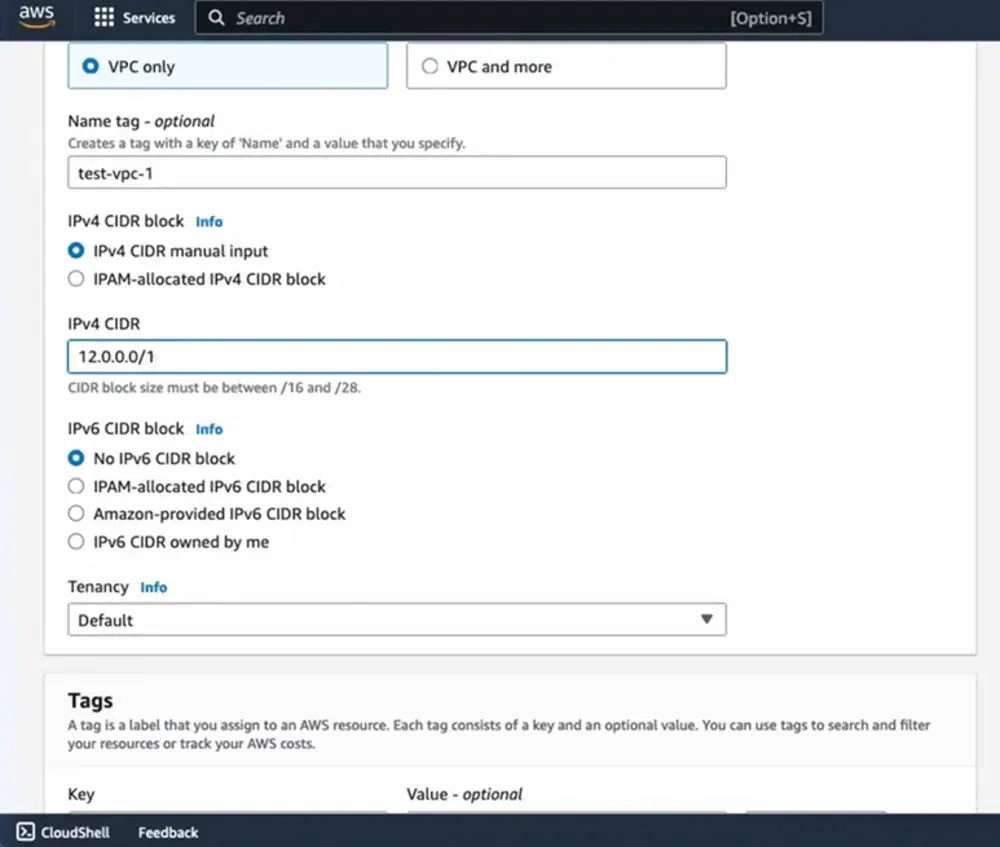
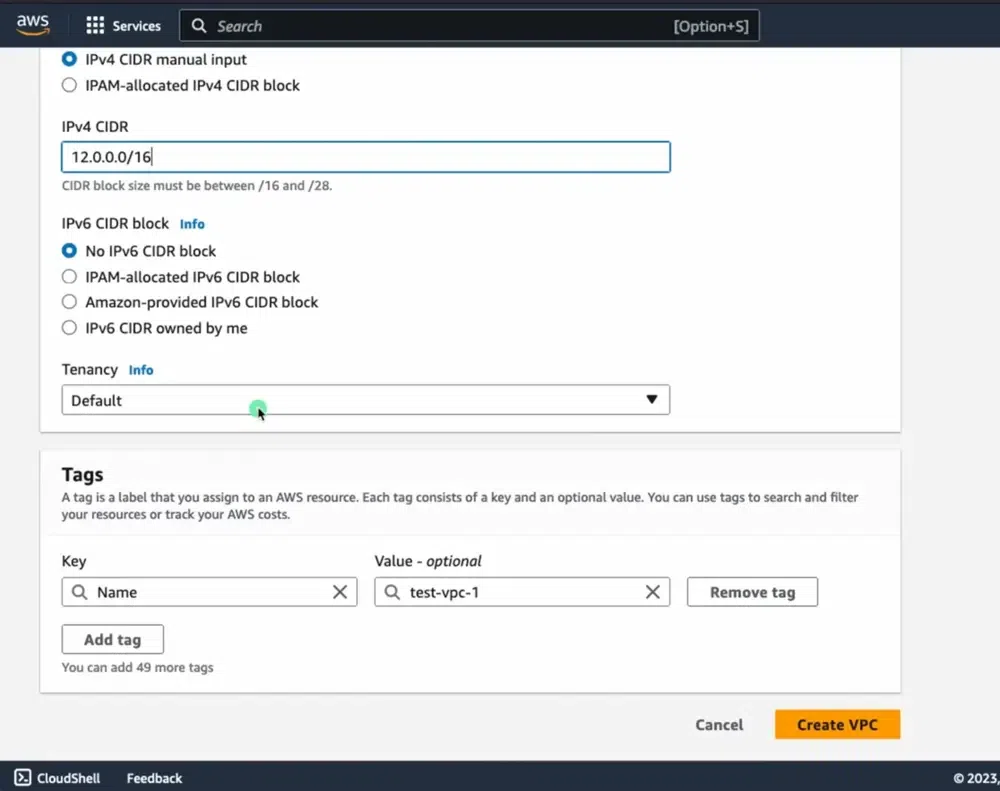
- Similarly define and create second vpc with name test-vpc-2 . Ensure that the CIDR of test-vpc-1 and test-vpc-2 doesn't overlay.
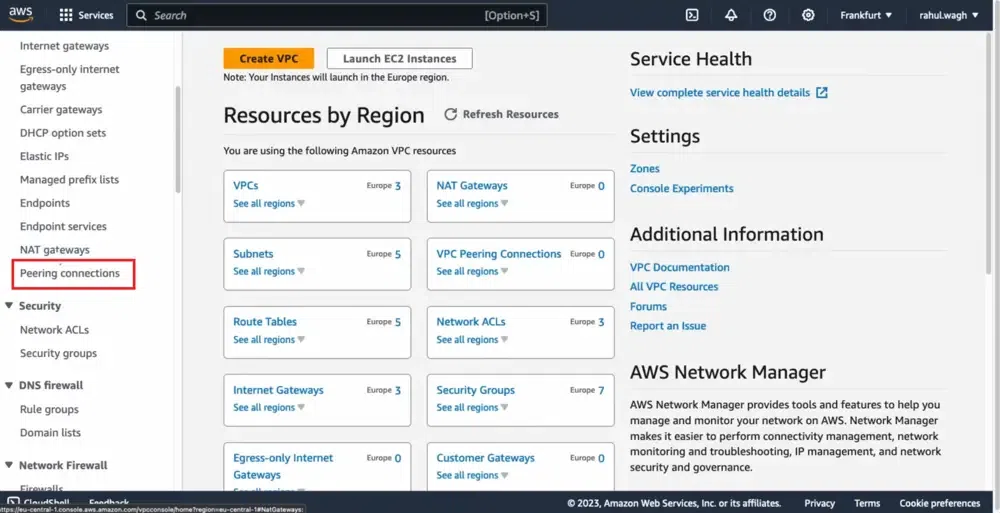
Step 3: Select "Peering Connections"
- Navigate to VPC Peering, and click on create VPC peering button.
- Provide the accepter VPC name and receiver VPC name.
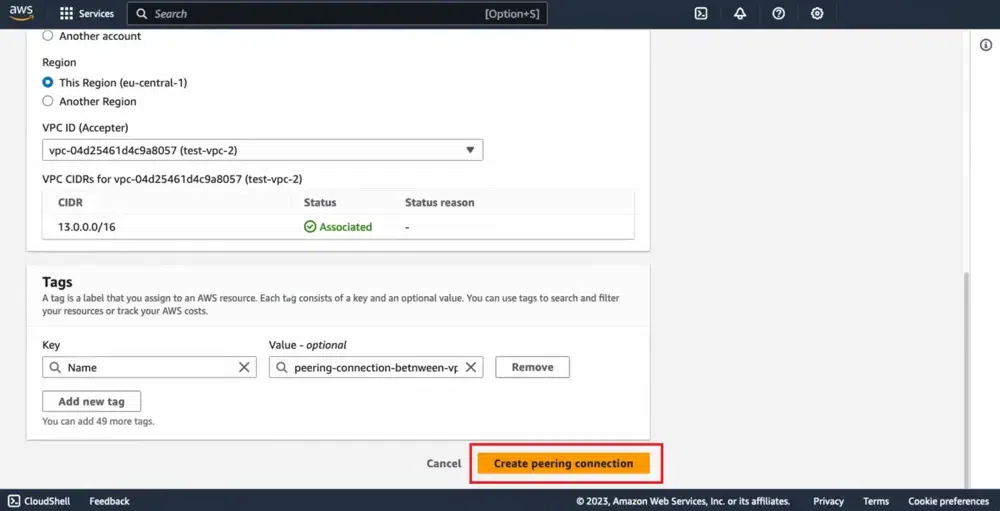
Step 3: Click "Create Peering Connection"
- After creating the vpc peering connection, it will be in pending status .
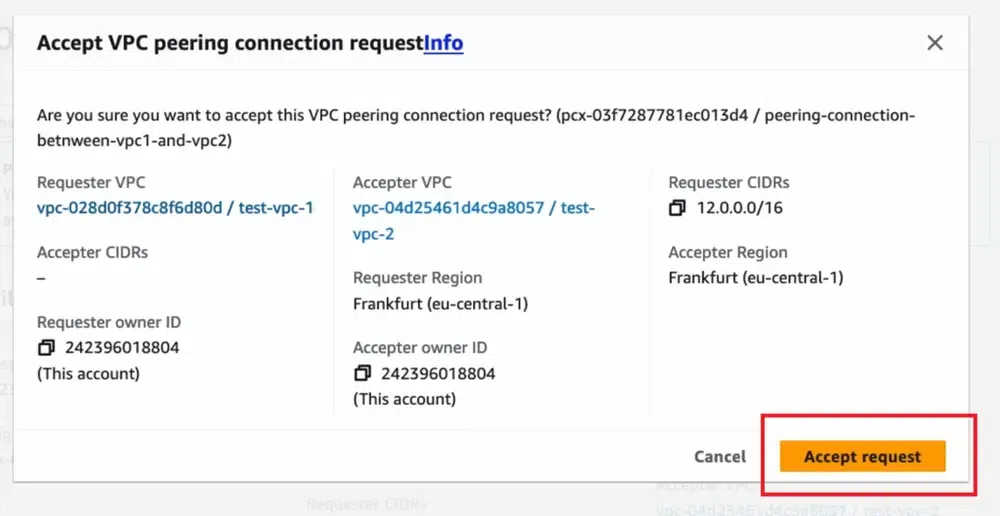
Step 4: Accept Peering Connection
- Now, from the myvpc2 aws account, go to vpc peering dashboard, click on the accept request and accept the peering connection.
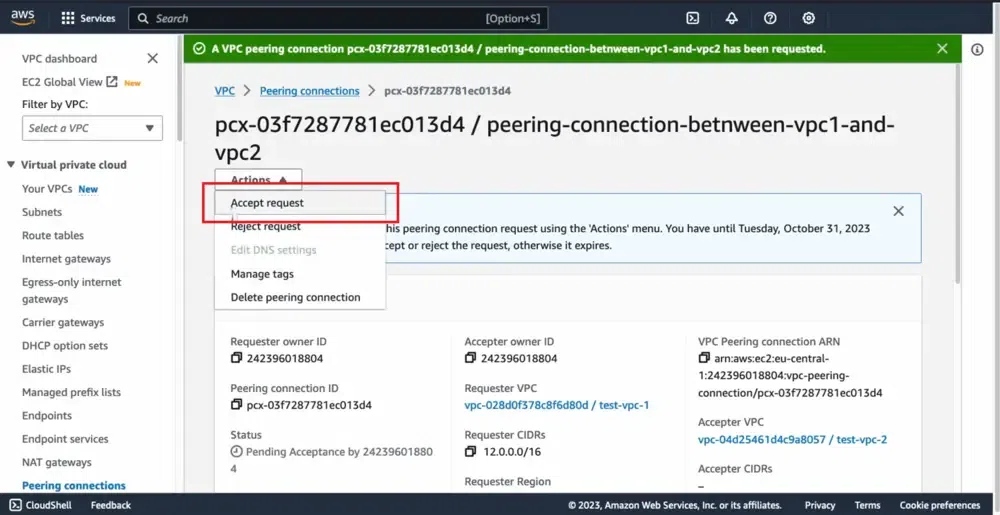
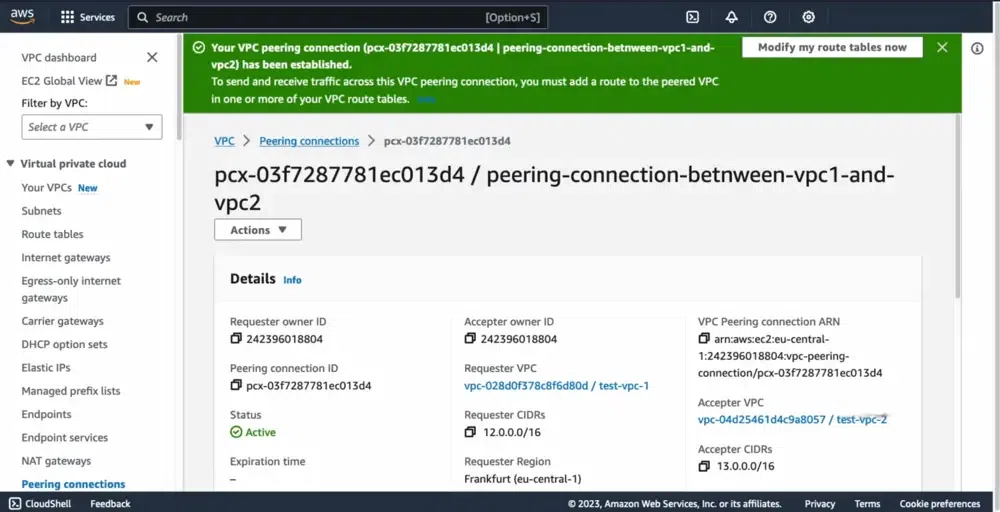
Step 5: Successful VPC Peering Connection
- After once the myvpc2 network accepts the request, the VPC peering connection will become active in status.
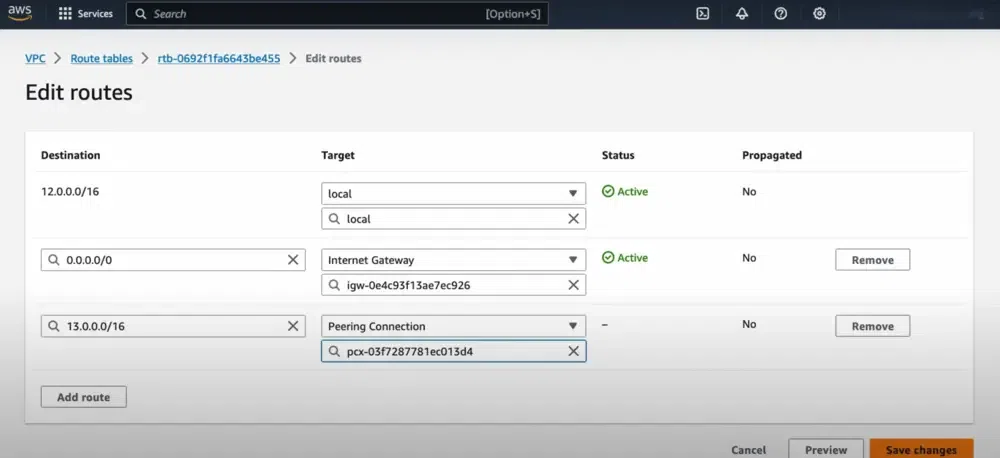
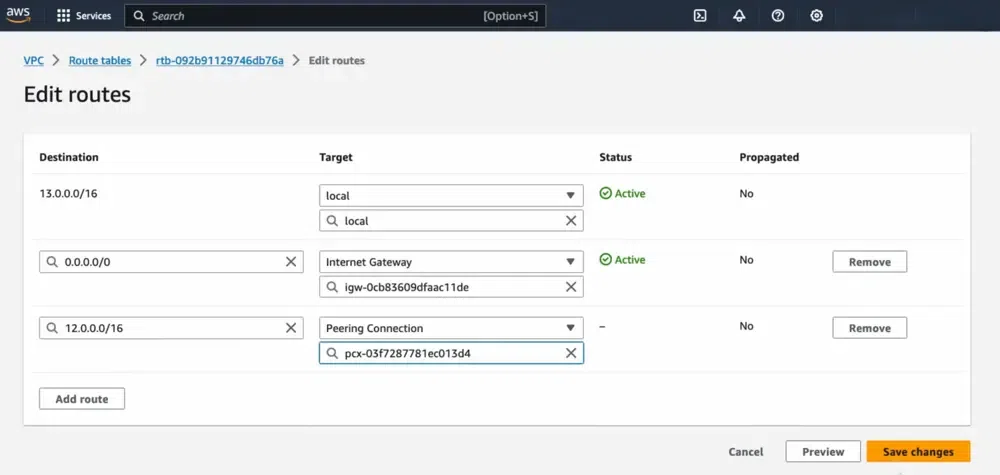
Step 6: Update Route Tables (if necessary)
- Ensure that the route tables for both VPCs are updated to include routes for each other's CIDR blocks, pointing to the peering connection.
Step 7: Verify Connectivity
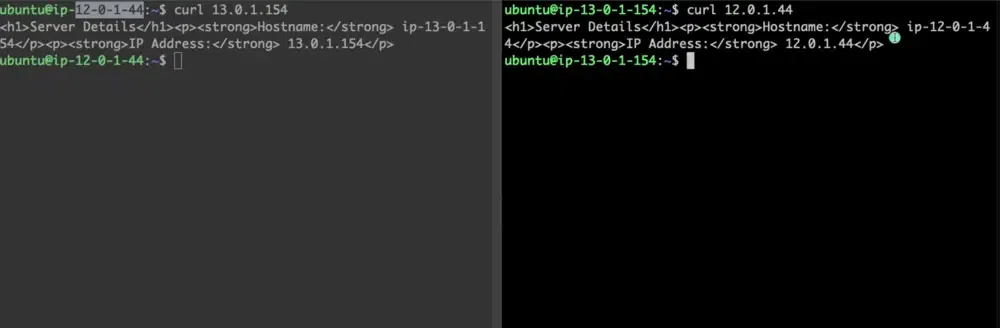
- Now, Create an instance on each vpc and try on pinging the private IP of instance on each other instance.
- If they are successfully pinging then you have established VPC peering successfully.
Sometimes we need to allow resources in different VPCs to exchange data based upon the architecture of the service. Regardless of any specific need, using VPC peering is a great way of extending your VPC design.
Note: When you start to have a lot of peering connections between multiple VPCs, in multiple regions, across multiple AWS accounts, managing the connections. When it starts to get difficult, it is time to start looking at moving the existing peering connections to Transit Gateway and managing the connections there.
VPC Peering vs. Transit Gateway
This is the classic "Build vs. Buy" networking decision.
| Feature | VPC Peering | AWS Transit Gateway |
|---|---|---|
| Topology | Mesh (Point-to-Point). | Hub-and-Spoke (Central Router). |
| Transitive? | No. A cannot talk to C via B. | Yes. A talks to C through the Gateway. |
| Management | Decentralized. Hard to manage at scale (10+ VPCs). | Centralized. Easy to manage hundreds of VPCs. |
| Bandwidth | Unlimited (limited only by instance type). | 50 Gbps per attachment. |
| Latency | Lowest (Direct path). | Slightly higher (Extra hop). |
| Cost | Low (Data transfer only). | High (Hourly attachment fee + data processing). |
Use VPC Peering for simple, high-bandwidth connections between 2-3 VPCs (e.g., App <-> DB). Use Transit Gateway for enterprise networks connecting dozens of VPCs and on-premises VPNs.
AWS VPC Peering Latency
AWS VPC Peering generally offers low level latency communication between the peered VPCs that are in same region. The traffic flows over the network, latency is generally minimal making it suitable for real-time applications and services. The latency is generally depends on the factors such as geographical distances between VPCs and potential network congestion which can slightly affect latency. AWS VPC peering is designed for efficient and reliable connectivity with minimal latency for inter-VPC communication.
AWS VPC Peering Bandwith
AWS VPC Peering connections offers scalable and high-bandwidth communication between peered VPCs. The bandwidth between the AWS VPCs depends on type of instances and its network capabilities of communication. AWS Direct Connect or AWS VPN connections can be used further for enhancing bandwidth between VPCs and on-premises networks also if needed.
Important Limitations
- Overlapping CIDRs: You cannot peer two VPCs with overlapping IP ranges (e.g., 10.0.0.0/16 and 10.0.0.0/16). This is a hard limit.
- Cross-Region Security Groups: You can reference a security group ID from another VPC (e.g., allowing traffic from sg-12345) ONLY if they are in the same region. For cross-region peering, you must use CIDR blocks in your rules.
- Jumbo Frames: Supported for same-region peering, but check instance type compatibility.
Pricing for a VPC Peering Connection
The following tabular format discusses the pricing details of VPC Peering:
Component | Description | Cost |
|---|---|---|
VPC Peering Connection | It used for establishment of VPC Peering connection | $0.01 per GB |
Data Transfer between VPCs | It used for transfering the data between VPCs | $0.02 per GB |
NAT Gateway | If it is used for data transfer | Additional fee |
Data Processing | If data processing has done in VPC | Variable |
Support | It used for provding support to VPC Connection | Variable |
Use Cases
- Shared Services: A central "Tools" VPC (Jenkins, Monitoring) peered to multiple "App" VPCs.
- Data Transfer: Replicating a database from a Production VPC to an Analytics VPC for reporting.
- Mergers & Acquisitions: Quickly connecting two companies' cloud networks (provided CIDRs don't overlap!).